When you self-custody your Bitcoin with Passport, you are in full control of your money. This means you are also completely responsible for ensuring your Bitcoin is backed up safely and securely, such that your Bitcoin is not lost easily to any single point of failure.
¶ Video Explainer
The following video explains:
- The two different types of backups Passport offers
- How to create, store and recover from a Seed Word backup
- How to create, store and recover from an Encrypted Backup
- The pros and cons of each backup type
¶ Types of Passport Backup
¶ Encrypted SD Card Backup
By default, Passport creates a backup file containing your seed words and device settings. This data is saved, fully encrypted, to a microSD card. We supply one industrial grade microSD with Passport, but you can easily obtain extra from any typical electronics store.
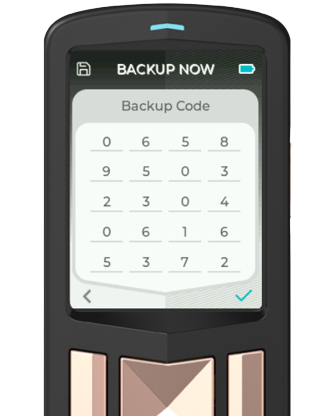
This backup file is encrypted with your Backup Code, shown to you upon setup. The Backup Code is 20 digits long and should be written down on the card provided with the device. You can download additional copies of the card here.
The architecture of this Backup solution dictates that both the microSD card and the Backup Code are required for recovery, it is crucial for them to be stored separately.
.png)
For more info on why we love the Encrypted Backup solution, check out our blog post.
TLDR - Encrypted backups allow you to create multiple secure backups to remove any single point of failure, but more advanced users might also choose to use a Seed Word backup for extra protection from physical damage.
¶ Seed Words
Users choosing the Envoy setup method will not be shown their seed words upon setup, but can view them any time, once logged in to Passport, in Settings > Advanced > View Seed Words. More advanced users choosing the manual setup will be shown these words as part of the set up process.
Your seed words can be written down on the card provided with the device. You can download additional copies of the card here.
Most Bitcoin seed word backups are stored in plain text. This makes them extremely sensitive information. Anyone with access to them can steal your Bitcoin! Choose your storage location of this type of backup extremely carefully.
¶ Backup Creation and Storage
¶ Encrypted SD Card Backup
Users choosing the Envoy setup method will be guided through the creating their first encrypted microSD card backup. This includes writing down their 20 digit backup code.
All Passport users can create addition encrypted backups to an unlimited number of new microSD cards by heading to Settings > Backup > Backup Now. The Backup Code can also be viewed at any time from the same Backup menu.
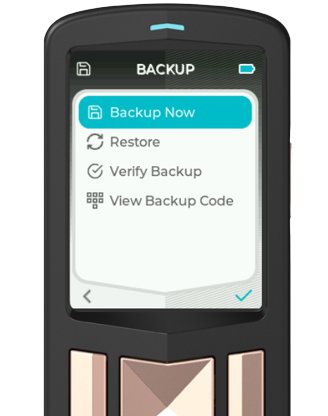
Upon any device state change, such as Account addition or removal, or upon the import of a multisig configuration, Passport will automatically create a new, additional Encrypted Backup if there is a microSD inserted into the device. Older files are never overwritten and each new Backup file is appended with a unique number. Higher number = Newer backup.
¶ Physical SD Storage
How many Encrypted microSD card Backups you make will depend entirely on how many different locations you feel comfortable storing them at. Because each SD card is encrypted using a strong encryption standard, these SD cards are useless to anyone that does not have access to your 20 digit backup code.
To remove the threat of a single storage location being compromised, it is good practice to keep at least 1 microSD away from your residence, potentially with a friend of family member. SD cards are small commodity items that are very easy to store covertly, so keeping multiple offsite copies makes sense, but this is very dependent on you and your personal circumstances.
Remember, never store the Backup Code with the microSD card.
¶ Backup Code Storage
As with the physical storage of the microSD card, how and where you store copies of your Backup Code is very dependent on you, your personal circumstances, but also your technical abilities. Once again you should look to remove single point of failures, so having more than one location is good practice. Here are some commonly used approaches:
- Writing down the code on the backup card provided with Passport and storing at home in a safe.
- Giving a hand written copy of the backup code to a friend or family member (ensuring they are not also storing an encrypted SD card).
- Storing the backup code in an online Password Manager like Bitwarden.
Remember, never store the encrypted microSD card in the same location as your Backup Code.
¶ Seed Words Backup
The method of creating a physical backup of your Seed Words will depend on the solution you choose to store them in. As a reminder, you can view your seed words at any time, once logged in to Passport, in Settings > Advanced > View Seed Words.
We provide a physical card in the box with Passport for you to write them down on, but this solution is not resistant to fire or water damage, so please do not make this your only backup solution.
¶ Physical Seed Storage
We recommend storing your seed words using a medium that is resistant to fire, water and corrosion etc.
Where you store your seed words should be a deeply thought out decision. Physical access to this single item grants full access to all of your Bitcoin. This can be mitigated by the use of a passphrase, but this is an advanced feature that should be carefully considered.
Keeping multiple copies of your plain text seed creates multiple single points of failure. Anyone with access to any copy of your seed words, has access to all of the Bitcoin in that wallet.
¶ Backup Recovery
¶ Encrypted SD Card Recovery
To recover your wallet using a Passport generated Encrypted Backup, you will both the Backup Code and a microSD card containing your encrypted backup file. Here's how to do it on Passport:
- Power on the new or wiped device and when at the Create Seed screen, choose Restore Backup.
- Insert the microSD card containing the backup into the top of Passport.
- Choose the backup file from the list.
- Enter the 20 digit backup code
That's it, your Passport should now look identical to the last time the backup was created.
If for any reason you want or need to recover from an encrypted backup file without using Passport, you can follow the instructions outlined here. Be aware that using this method will expose your seed to an internet connected device, which brings with it far greater potential risk factors. This method should only be carried out in absolute emergencies (for example if you lost access to Passport and need to spend funds quickly).
¶ Seed Words Recovery
Here's how to recover your wallet using your Seed Word backup on Passport:
- Power on the new or wiped device and when at the Create Seed screen, choose Restore Seed.
- Choose the length of the seed to be restore. Generally this will be 24 words.
- Enter your seed words. Passport uses predictive text entry to make this process as fast as possible. For instance, to enter car, simply type 2-2-7. Passport will display all words associated with that key combination for you to choose from.
That's it, your Passport wallet is now restored. If you were using additional accounts, those will need to be recreated on device. If you were using the seed as part of a multisig wallet, the configuration file will need to be re-imported. Finally, if you had any keys derived within the Key Manager extension, those will need to be recreated too.
If for any reason you want or need to recover from seed words without using Passport, you can import your BIP39 compliant BIP39 seed words into any compatible hardware or software wallet. Be aware that using this method will expose your seed to an internet connected device, which brings with it far greater potential risk factors. This method should only be carried out in absolute emergencies (for example if you lost access to Passport and need to spend funds quickly).
¶ Backups FAQ
¶ How many backup SD cards should be made?
This is very dependent on you, but generally speaking you should have at least two. Read more details here.
¶ How do Automatic Backups work?
Upon any device state change, such as Account addition or removal, or upon the import of a multisig configuration, Passport will automatically create a new, additional Encrypted Backup if there is a microSD inserted into the device. Older files are never overwritten and each new Backup file is appended with a unique number. Higher number = More recent backup.
If you do not want Automatic Backups to be saved to an SD card you use for transaction signing, please do not leave this microSD card inserted to Passport. If you forget and Passport automatically writes an Auto Backup to your SD, you can remove it on deivce by heading to Settings > Advanced > microSD > List Files > Enter the backups folder > Select the file to be deleted > Click Delete.
¶ Should I keep the SD card containing my Encrypted Back inside Passport?
Ideally any SD card containing an Encrypted Backup should be kept out of sight, away from Passport. This provides some plausible deniability around the purpose of the SD card.
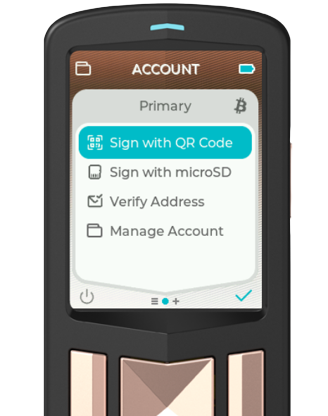
¶ Can I use the same SD card for my Backup and signing transactions?
You can, but it is advised to use dedicated microSD card(s) for your backups and to use a separate microSD card for passing transactional information via PSBTs. If you prefer not to use Passport's Sign with QR feature of course!
¶ Are SD cards sensitive to heat, humidity, water/flooding?
Yes. Your encrypted microSD card should be stored in a secure, cool and dry place far away from obvious threats. We ship an industrial grade microSD card with Passport, but there are no guarantees on the exact amount of damage these can withstand. The nature of this type of encrypted backup affords users the ability to securely store multiple copies at different locations, such that if one were to succumb to damage by heat or water, it would not result in a catastrophic loss of funds.
¶ Should I copy my backup to my computer?
Unless you are an advanced user, proficient in securing computers effectively, your encrypted backup file(s) should not be stored on a computer. Doing so potentially exposes them to remote extraction from anyone sophisticated enough able to connect to your computer. Whilst an attacker could not easily break the strong encryption of the file, they could easily copy and distribute it 1000s of times over.
¶ Should I put my password in a password manager if the backup is stored on the same computer?
We would not advise that for the reasons outlined above.
¶ Where should my password be stored?
We cover that here.
¶ How and how often should I test the backup of an SD card?
We recommend you test the backups at least once annually. Learn how to do that here.
¶ Should I backup the BIP39 phrase also?
If you can satisfy yourself of the trade-offs outlined here, and/or you want a simple offline backup that is completely redundant of Passport, yes.
¶ How do I restore from an encrypted backup without Passport?
We cover two methods of doing this in detail here.